Module 4: The Six Dimensions of Maturity
Learning Objectives
- Define each of the six dimensions in plain language.
- Identify Level 1-5 indicators for each dimension from artifact evidence.
- Apply the Floor Constraint Principle to a mixed-score profile.
- Read and interpret a Maturity Map radar chart.
4.1 OverviewCore
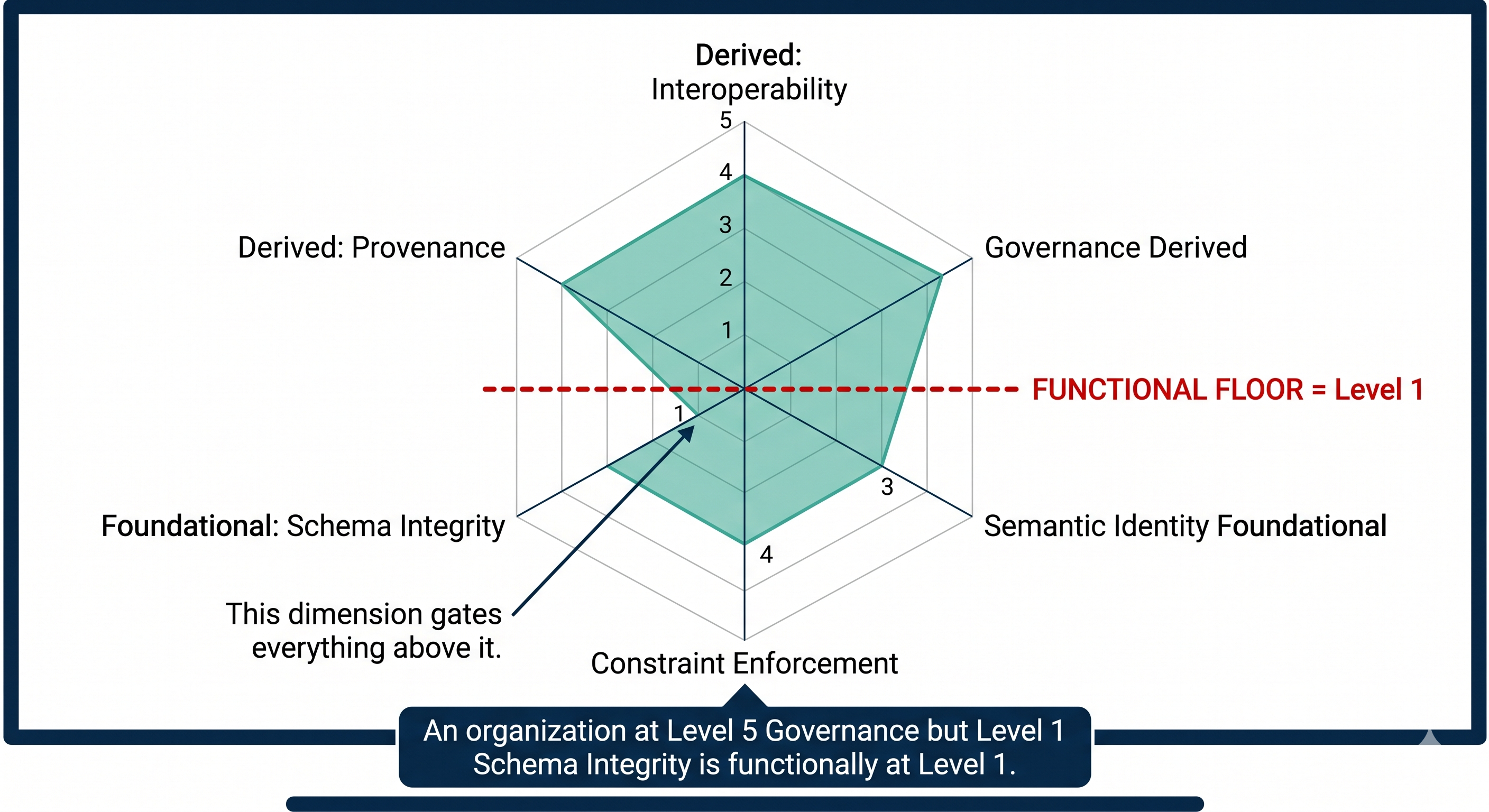
The SDC Maturity Map assesses six dimensions, each scored 1-5. Three are foundational (the floor) and three are derived (capped by the foundation).
| # | Dimension | Category | Floor? |
|---|---|---|---|
| 1 | Schema Integrity | Foundational | Yes |
| 2 | Constraint Enforcement | Foundational | Yes |
| 3 | Semantic Identity | Foundational | Yes |
| 4 | Provenance | Derived | No |
| 5 | Interoperability | Derived | No |
| 6 | Governance | Derived | No |
The Floor Constraint
A derived dimension cannot exceed the minimum of the three foundational dimensions. A client cannot have trustworthy provenance over data with no schema integrity. They cannot have meaningful interoperability without semantic identity. They cannot govern what they cannot constrain.
4.2 Schema IntegrityCore
Definition: The degree to which data structures are explicitly defined, versioned, and enforced at write time.
What you are looking for: Is there a schema? Is it the same schema everyone uses? Does it change? When it changes, do existing records get migrated or do they silently break?
Levels
- Level 1 - Ad Hoc: Data lives in spreadsheets and free-text fields. Column names vary between files. No formal definitions.
- Level 2 - Documented: A data dictionary exists somewhere. It is mostly current. Some systems enforce it; others don't.
- Level 3 - Enforced (On Track): A canonical schema is enforced at write time by at least the primary system. Versions are tracked. Schema changes go through review.
- Level 4 - Integrated: All systems share a single source-of-truth schema. Migrations are automated. Schema changes trigger downstream notifications.
- Level 5 - Federated: Schemas compose across organizational boundaries via shared reference models. Cross-org joins work without translation layers.
Evidence to ask for: A copy of the data dictionary. A recent ALTER TABLE log. An example of a field that was renamed and how downstream systems handled it.
4.3 Constraint EnforcementCore
Definition: The degree to which validation rules travel with the data and execute at the point of writing.
Levels
- Level 1: Constraints exist only in the heads of long-tenured employees. New hires reinvent them.
- Level 2: Constraints documented in a wiki. Enforced by occasional batch jobs that produce reports nobody reads.
- Level 3: Constraints enforced by the primary system at write time (NOT NULL, CHECK, foreign keys). Violations rejected.
- Level 4: Constraints expressed declaratively (Schematron, SHACL, JSON Schema) and re-used across multiple systems.
- Level 5: Constraints versioned alongside data. Historical records validate against the constraint version that was active when they were written.
Evidence: A constraint document. A query that finds rows violating the documented rules (count > 0 means Level ≤ 2).
4.4 Semantic IdentityCore
Definition: The degree to which every data element has a stable, unambiguous identifier whose meaning does not depend on context.
Levels
- Level 1: Auto-increment integer IDs scoped to a single database. "Customer 47" means different people in different systems.
- Level 2: UUIDs or GUIDs used in some places. Not universally adopted. Joins still rely on natural keys.
- Level 3: Stable identifiers (UUID, CUID, ULID) used for all primary entities. No reuse after deletion.
- Level 4: Identifiers are URI-formed and dereferenceable within the organization. Cross-system joins use the same ID space.
- Level 5: Identifiers are globally unique, sovereign, and resolvable across organizational boundaries. CUID2-style identifiers bound to data packets.
Evidence: Pull a record. Ask "if I gave this ID to your billing system, would it find the same entity?" If the answer involves a translation table, you are at Level ≤ 2.
4.5 ProvenanceCore
Definition: The degree to which every data value can be traced to its origin, author, time, and conditions of capture.
Levels
- Level 1: created_at and updated_at columns. No author. No conditions.
- Level 2: Audit log captures who-changed-what for some tables. Gaps exist. Logs purged after N days.
- Level 3: Append-only audit log for all sensitive tables. Author, timestamp, and previous value captured.
- Level 4: Provenance graph spans system boundaries. You can trace a dashboard number back through every transformation to the source row.
- Level 5: Provenance is cryptographically signed and tamper-evident. Suitable for regulatory or legal evidence.
Floor constraint reminder: Provenance cannot exceed min(Schema Integrity, Constraint Enforcement, Semantic Identity). You cannot trace what you cannot identify.
4.6 InteroperabilityCore
Definition: The degree to which data can cross organizational or system boundaries without reinterpretation.
Levels
- Level 1: Data shared via emailed spreadsheets. Receiving party manually reformats.
- Level 2: Point-to-point APIs. Each integration is bespoke.
- Level 3: Standard formats (JSON-LD, FHIR, OData) used for at least one interface.
- Level 4: Multiple systems exchange data via shared standards with no per-system mapping layer.
- Level 5: Data carries enough self-description that an unknown receiver can interpret it correctly using only published standards.
Evidence: How long does it take to onboard a new partner? If the answer is "weeks," you are at Level ≤ 2.
4.7 GovernanceCore
Definition: The degree to which data quality rules are documented, enforced, audited, and improved over time.
Levels
- Level 1: No data governance role exists. Quality issues handled ad hoc.
- Level 2: A data steward exists. Policies documented. Enforcement uneven.
- Level 3: Quality metrics tracked. Violations trigger remediation workflows. Quarterly review.
- Level 4: Quality SLAs published. Stakeholders accountable. Continuous monitoring.
- Level 5: Governance integrated with provenance and constraint layers. Policy-as-code. Automated compliance reporting.
The context graph connection: Governance at Level 5 means the client's data carries its own decision traces. Every state transition in a workflow is recorded with who authorized it, under what authority, and what the state of the data was at the moment of the decision. This is what the industry is now calling a "context graph" - a knowledge graph where the reasoning behind decisions is queryable and auditable, not just the outcomes. When you assess a client's Governance dimension, you are measuring how close they are to having a structurally governed context graph vs. a documentation binder that no agent can read.
4.8 Reading the Radar ChartIntermediate
A Maturity Map produces a six-axis radar chart. Three things to look for:
- Floor: What is the minimum of the three foundational dimensions? That is the client's effective ceiling on the derived dimensions.
- Inversion: Are the derived dimensions higher than the foundational ones? That is a red flag - it means the client is investing in the wrong layer.
- Asymmetry: Big gaps between adjacent dimensions usually indicate organizational silos.
A healthy intermediate client looks like a hexagon with all six points roughly equal at Level 3. An unhealthy one is a star shape with peaks at Governance and Interoperability and valleys at Schema and Identity.
Module 4 Quiz
0 of 4 answers reviewed
Continuing with Atlas Legal: The following scores are from your Atlas Legal assessment (see the full findings in exercises/case_atlas_legal.html). Apply the scoring rubric and the floor constraint principle.
You receive these scores from Atlas Legal:
- Schema Integrity: 2
- Constraint Enforcement: 2
- Semantic Identity: 1
- Provenance: 4
- Interoperability: 3
- Governance: 5
1. What is the effective ceiling on the derived dimensions? (See Section 4.1)
Level 1 - the minimum of the three foundational dimensions. Semantic Identity at Level 1 is the binding constraint.
Effective scores: Provenance functionally 1 (scored 4), Interoperability functionally 1 (scored 3), Governance functionally 1 (scored 5). The organization is functionally at Level 1 across all derived dimensions.
2. The client is proud of their Governance score. How do you explain to them, without crushing morale, that it is misleading? (See Section 4.7)
Frame it as aspiration vs. foundation: "Your Governance score tells us your team has built mature policies. What the Maturity Map reveals is that those policies are governing data that doesn't yet have the structural foundation to make the governance enforceable."
Use the metaphor: "You've built excellent traffic laws, but the roads don't have lane markings yet. The laws are correct - they just can't be enforced until the infrastructure catches up."
Show the path: "If we bring Semantic Identity to Level 3, your Governance score immediately becomes real. The work you've already done pays off."
Never say "your score is wrong." Say "your score shows where you're heading. The Map shows what needs to happen to get there."
3. Which dimension would you recommend they invest in first, and why? (See Section 4.3)
Semantic Identity - it is the lowest foundational dimension (Level 1) and the binding constraint on everything else.
Sequence: (1) Semantic Identity 1->2 via CUID2 assignment, (2) Schema Integrity 2->3, (3) Constraint Enforcement 2->3. Only then do derived dimensions unlock above Level 2.
Common wrong answers: "Governance first" (the executive trap - governance over unstable identity is policy documentation, not enforcement). "Provenance first" (the sunk-cost trap - more detailed records about data you can't reliably track).
4. Sketch the radar chart. What shape does it form? What does that shape suggest about the organization? (See Section 4.8)
The chart forms a top-heavy or inverted triangle: derived dimensions extend far outward while foundational dimensions are pulled inward.
This suggests: "Beautiful policies over broken data." The organization invested in visible, executive-facing dimensions (governance, interoperability) while neglecting the structural foundation. Common in organizations that have been through compliance audits and responded with policy frameworks.
Quick win potential: Fixing Semantic Identity from 1 to 3 immediately unlocks the value of the governance work already done. The ROI on foundational investment is amplified by existing derived-dimension maturity.